

By Bill Hagerstrand, Director, Security Business, Marvell
Last year, Marvell announced that the Marvell LiquidSecurity family of cloud-based hardware security modules (HSMs) achieved FIPS 140-3, Level-3 certification from the National Institute of Standards and Technology. FIPS 140-3 certification is mandatory for many financial institutions and government agencies and, until then, had largely only been available with traditional self-managed, on-premises HSMs.
FIPS 140-3 certification also meant that cloud service providers could use LiquidSecurity HSMs to provide a wider range of security services to larger universe of customers.
Microsoft, which uses LiquidSecurity HSMs to power its Azure Key Vault and Azure Key Vault Managed HSM service, said it would begin to incorporate FIPS140-3 certified modules into its infrastructure.
This month, Microsoft began to offer single-tenant HSM services with FIPS 140-3 based services with LiquidSecurity in public preview.
“Every interaction in the digital world from processing financial transactions, securing applications like PKI, database encryption, document signing to securing cloud workloads and authenticating users relies on cryptographic keys. A poorly managed key is a security risk waiting to happen. Without a clear key management strategy, organizations face challenges such as data exposure, regulatory non-compliance and operational complexity,” Microsoft’s Sean Whalen wrote in the Azure Infrastructure blog. “An HSM is a cornerstone of a strong key management strategy, providing physical and logical security to safeguard cryptographic keys.
By Michael Kanellos, Head of Influencer Relations, Marvell
Marvell co-founder, Sehat Sutardja, was a visionary leader, brilliant engineer, and a cherished colleague and friend to many at Marvell.
Sehat’s journey began in Jakarta, Indonesia where he would build Van de Graaf generators and other devices with spare parts from his parents’ auto parts store. By 13, he was already a certified radio repair technician, showcasing his innate talent and curiosity. This early interest led him to pursue higher education in the United States, where he earned his bachelor’s degree in electrical engineering from Iowa State University, followed by a master’s and PhD in electrical engineering from the University of California, Berkeley.
Stephen Lewis, now a professor of electrical and computing engineering at UC Davis, described Sehat as a perfectionist in an article for IEEE Spectrum. As students, they were building analog-to-digital converters. The traditional way to make them involved using two capacitors, one twice the size as the other. “He figured out a way to do it with two identical capacitors, increasing the amplifier speed by increasing its feedback. We had a solution that worked, but he kept digging until he found a better way to do it.”
In 1995, Sehat, wife Weili Dai, and Sehat’s brother Pantas Sutardja founded Marvell Technology around a kitchen table. They chose the name Marvell because they wanted to build a company that could create ‘marvelous’ devices. The first product was a specialized read channel for hard drives that could be produced completely in silicon. Conventional wisdom was that the approach wouldn’t work, Sehat told students during a lecture at Berkeley in 2014. The device, however, reduced power consumption and production cost while elevating performance. Marvell soon became a trusted partner to many of the world’s leading technology companies.
As an inventor and co-inventor, Sehat held over 440 patents. He was recognized as the Inventor of the Year by the Silicon Valley Intellectual Property Law Association and named a Fellow of IEEE. He also received the Indonesian Diaspora Lifetime Achievement Award for Global Pioneering and Innovation and frequently spoke at events such as the International Solid State Circuits Conference about the future of semiconductor design and computing.
Beyond his professional accomplishments, Sehat was known for his humility, kindness, and generosity. He was a mentor to many, always willing to share his knowledge and insights. The Marvell team is grateful for his contributions and the legacy he leaves behind through his co-founding of our company.
By Bill Hagerstrand, Director, Security Business, Marvell
Payment-specific Hardware Security Modules (HSMs)—dedicated server appliances for performing the security functions for credit card transactions and the like—have been around for decades and not much has changed with regards to form factor, custom APIs, “old-school” physical user interfaces via Key Loading Devices (KLDs) and smart cards. Payment-specific HSMs represent 40% of the overall HSM TAM (Total Available Market), according to ABI Research1.
The first HSM was built for the financial market back in the early 1970s. However, since then HSMs have become the de facto standard for more General-Purpose (GP) use cases like database encryption and PKI. This growth has made HSM usage for GP applications 60% of the overall HSM TAM. Unlike Payment HSMs, where most deployments are 1U server form factors, GP HSMs have migrated to 1U, PCIe card, USB, and now semiconductor chip form factors, to meet much broader use cases.
The typical HSM vendors that offer both Payment and GP HSMs have opted to split their fleet. They deploy Payment specific HSMs that are PCI PTS HSM certified for payments and GP HSMs that are NIST FIPS 140-2/3 certified. If you are a financial institution that’s government mandated to deploy a fleet of Payment HSMs for processing payment transactions, but also have a database with Personally Identifiable Information (PII) data that needs to be encrypted to meet General Data Protection Regulation (GDPR) or California Consumer Privacy Act (CCPA), you would also need to deploy a separate fleet of GP HSMs. This would include two separate HW, two separate SW, and two operational teams to manage each. Accordingly, the associated CapEx/OpEx spending is significant.
For Cloud Service Providers (CSPs), the hurdle was insurmountable and forced many to deploy dedicated bare metal 1U servers to offer payment services in the cloud. These same restrictions that were forced on financial institutions were now making their way to CSPs. Also, this deployment model is contrary to why CSPs have succeeded in the past, which was to offer when they offered competitively priced services as needed on shared resources.
By Bill Hagerstrand, Director of Security Solutions at Marvell
InfoSec Global, a leader in cryptographic agility management analytics software, and Marvell, a leader in Cloud based HSMs (Hardware Security Modules), have partnered to enable visibility and security in the cloud.

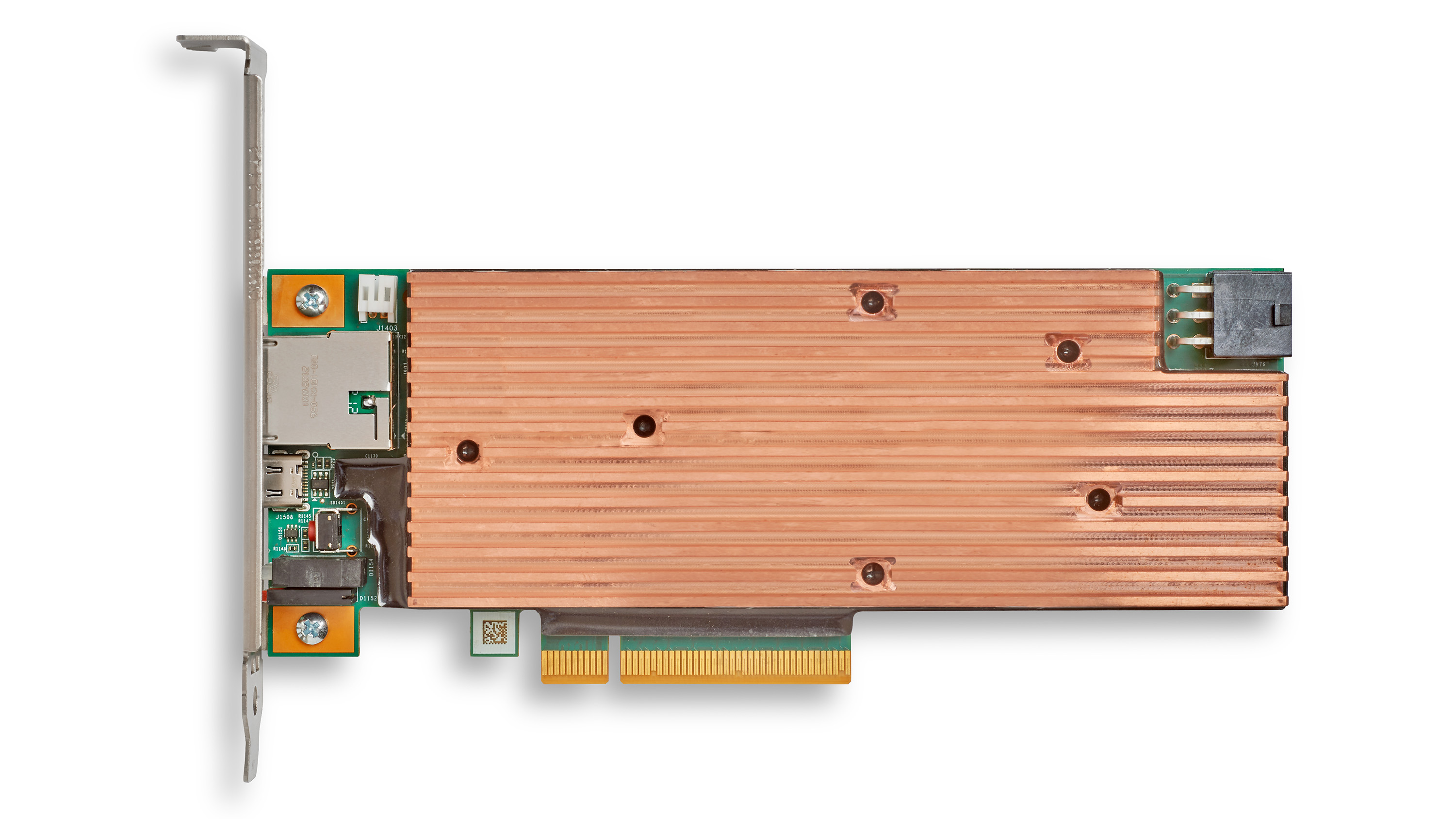
The Marvell® LiquidSecurity® family is a solution of hardware security modules (HSMs) based on a PCIe form factor instead of traditional 1U and 2U pizza boxes They are purposely designed to enable CSPs (Cloud Service Providers) to offer security services in a cloud environment. Not only does the smaller form factor and optimized processing of LiquidSecurity provide a path to reduce the cost, overhead, and rack space needed for performing encryption and key management, partitions and others performance features enable clouds to serve a large number of customers in a flexible manner.
By Todd Owens, Field Marketing Director, Marvell
While Fibre Channel (FC) has been around for a couple of decades now, the Fibre Channel industry continues to develop the technology in ways that keep it in the forefront of the data center for shared storage connectivity. Always a reliable technology, continued innovations in performance, security and manageability have made Fibre Channel I/O the go-to connectivity option for business-critical applications that leverage the most advanced shared storage arrays.
A recent development that highlights the progress and significance of Fibre Channel is Hewlett Packard Enterprise’s (HPE) recent announcement of their latest offering in their Storage as a Service (SaaS) lineup with 32Gb Fibre Channel connectivity. HPE GreenLake for Block Storage MP powered by HPE Alletra Storage MP hardware features a next-generation platform connected to the storage area network (SAN) using either traditional SCSI-based FC or NVMe over FC connectivity. This innovative solution not only provides customers with highly scalable capabilities but also delivers cloud-like management, allowing HPE customers to consume block storage any way they desire – own and manage, outsource management, or consume on demand.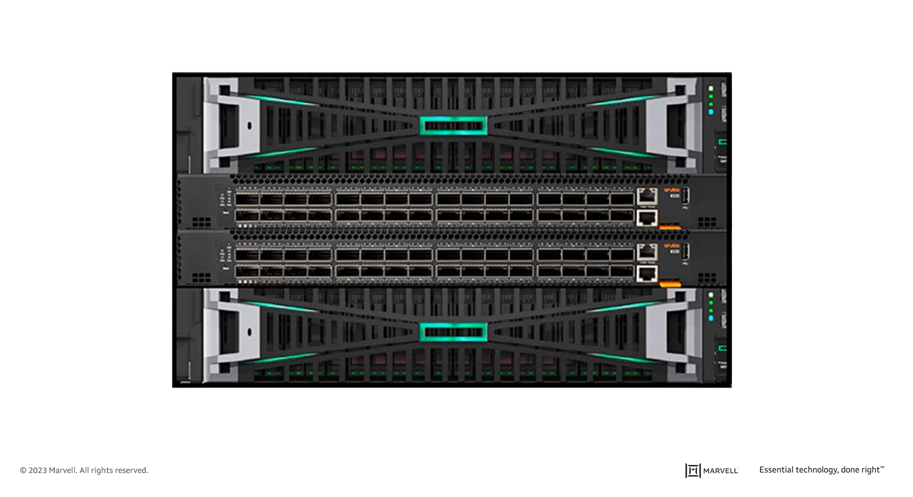 HPE GreenLake for Block Storage powered by Alletra Storage MP
HPE GreenLake for Block Storage powered by Alletra Storage MP
At launch, HPE is providing FC connectivity for this storage system to the host servers and supporting both FC-SCSI and native FC-NVMe. HPE plans to provide additional connectivity options in the future, but the fact they prioritized FC connectivity speaks volumes of the customer demand for mature, reliable, and low latency FC technology.