By Bill Hagerstrand, Security Solutions BU, Marvell
Time to grab a cup of coffee, as I describe how the transition towards open, disaggregated, and virtualized networks – also known as cloud-native 5G – has created new challenges in an already-heightened 4G-5G security environment.
5G networks move, process and store an ever-increasing amount of sensitive data as a result of faster connection speeds, mission-critical nature of new enterprise, industrial and edge computing/AI applications, and the proliferation of 5G-connected IoT devices and data centers. At the same time, evolving architectures are creating new security threat vectors. The opening of the 5G network edge is driven by O-RAN standards, which disaggregates the radio units (RU), front-haul, mid-haul, and distributed units (DU). Virtualization of the 5G network further disaggregates hardware and software and introduces commodity servers with open-source software running in virtual machines (VM’s) or containers from the DU to the core network.
As a result, these factors have necessitated improvements in 5G security standards that include additional protocols and new security features. But these measures alone, are not enough to secure the 5G network in the cloud-native and quantum computing era. This blog details the growing need for cloud-optimized HSMs (Hardware Security Modules) and their many critical 5G use cases from the device to the core network.
By Kim Markle, Director Influencer Relations, Marvell
Wind River and Marvell have collaborated to create an open, virtualized Radio Access Network (vRAN) solution for communication service providers (CSPs) that offers cloud scalability with the features, performance, and energy efficiency of established 5G networks. The collaboration integrates two complementary, industry-leading technologies—the Marvell® OCTEON® 10 Fusion 5G baseband processor and the Wind River Studio cloud software—to provide the carrier ecosystem a deployment-ready vRAN platform built on technologies that are widely proven in 5G networks and data centers.
CSPs aim to leverage established IT infrastructure for enhanced service agility and streamlined DevOps in the cloud-native RAN. Marvell's OCTEON 10 Fusion processor supports these goals with programmability based on open-source, industry-standard interfaces and integration with leading cloud software platforms such as Wind River Studio.
To ensure open-source distribution of Wind River Studio software, OCTEON 10 Fusion software drivers are being used by StarlingX, an open development and integration project. Marvell’s drivers enable Wind River Studio software to communicate with and control the OCTEON 10 Fusion processor. This facilitates developer access to an optimized vRAN system that offers new options for CSPs and helps to expand the carrier ecosystem of RAN and data center hardware and software suppliers, as well as system integrators.
By Matt Bolig, Director, Product Marketing, Networking Interconnect, Marvell
There’s been a lot written about 5G wireless networks in recent years. It’s easy to see why; 5G technology supports game-changing applications like autonomous driving and smart city infrastructure. Infrastructure investment in bringing this new reality to fruition will take many years and 100’s of billions of dollars globally, as figure 1 below illustrates.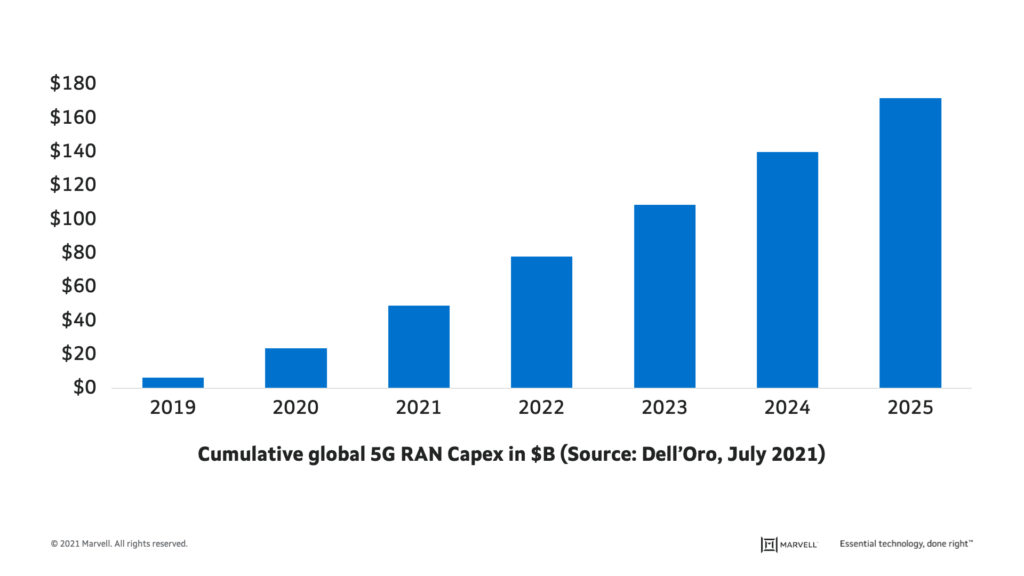
Figure 1: Cumulative Global 5G RAN Capex in $B (source: Dell’Oro, July 2021)
When considering where capital is invested in 5G, one underappreciated aspect is just how much wired infrastructure is required to move massive amounts of data through these wireless networks.
By Marvell, PR Team
Last week, Moor Insights and Futurum Research kicked off The Six Five Summit, a virtual, on demand event focused on the latest developments and trends in digital transformation. Marvell was thrilled to join alongside the world’s leading technology companies to share insights on strategy, innovation and where the industry is heading.
Marvell’s Raghib Hussain, President, Products and Technologies participated in the event’s Cloud and Infrastructure Day to discuss the evolution of the cloud data center including the shift from application-specific to data-centric compute. In his presentation, “Accelerating the Cloud Data Center Evolution,” Raghib focuses on how scalability, performance and efficiency are driving technology infrastructure requirements and why optimized and customized silicon solutions are the future of the cloud.
By Gidi Navon, Senior Principal Architect, Marvell
Enterprise networks are changing, adapting and expanding to become a borderless enterprise. Visibility tools must evolve to meet the new requirements of an enterprise that now extends beyond the traditional campus — across multi-cloud environments to the edge.
Copyright © 2025 Marvell, All rights reserved.